Learn About Application Protection
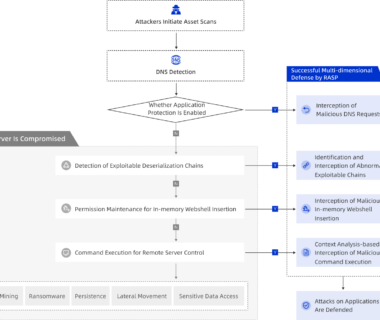
Overview The application protection feature is developed based on the runtime application self-protection (RASP) technology. This feature can detect attacks and provide self-protection during application runtime. You do not need to modify code to use the application protection feature. You need to only install the RASP agent on the servers or containers on which your […]